The Existential Business Threat – CMMC Series Part 2
Who Is Impacted by CMMC and the Key Timelines You Need to Know
Welcome back to our CMMC series, where we’re breaking down the Cybersecurity Maturity Model Certification (CMMC) program in practical terms for defense contractors. In Part 1, we covered the fundamentals: what CMMC is, its origins in protecting Federal Contract Information (FCI) and Controlled Unclassified Information (CUI), and why it represents a significant shift for the Defense Industrial Base (DIB). Now, let’s address the two questions on every contractor’s mind: Who exactly needs to comply, and when do these requirements take effect?
As we sit in January 2026, the phased rollout is well underway. The DoD’s final rule took effect in late 2025, and requirements are now appearing in solicitations and contracts. Compliance is no longer a future concern—it’s a present reality for many in the supply chain.
Who Is Impacted by CMMC Timelines?
CMMC isn't a blanket requirement for every company—it's targeted at those in the DoD ecosystem where data security directly impacts national defense. Specifically for Level 2 (the focus for most contractors handling CUI), the net is cast wide but precise. Here's a breakdown of the key players who need to pay attention:
- Prime Contractors: If you're a major player like a top-tier aerospace firm or systems integrator bidding on DoD contracts, Level 2 is non-negotiable for any work involving CUI. This includes giants managing multi-billion-dollar programs, where compliance ensures you can continue leading the charge in innovation without risking contract ineligibility.
- Subcontractors and Tiered Suppliers: Small and mid-sized businesses often form the backbone of the DIB supply chain. Whether you’re fabricating components for military vehicles, providing specialized machining, or supplying raw materials, if CUI flows through your systems (e.g., design specs or test data), you’re in scope. Many subs are feeling the pressure as primes pass down these requirements to avoid chain-wide vulnerabilities.
- Manufacturers in Defense Tech: Companies building hardware—from electronics to munitions—must comply if their processes involve CUI. This extends to emerging sectors like additive manufacturing or drone tech, where digital blueprints and intellectual property are prime targets for cyber threats.
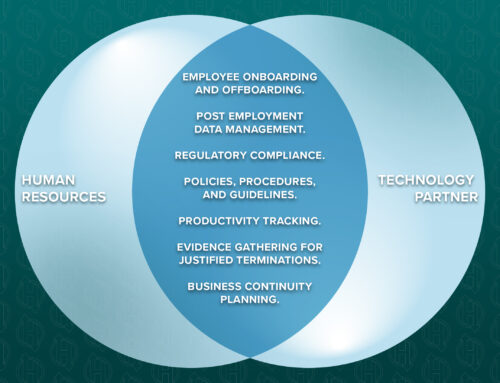
- IT and Managed Service Providers: If your firm handles cloud storage, network management, or cybersecurity for DoD-related clients, Level 2 certification is essential. This group is growing rapidly as more contractors outsource IT, but it also means you’re accountable for safeguarding CUI in transit or at rest.
- Engineering and Professional Services Firms: Consultants, engineers, or firms offering design, simulation, or advisory services under DoD umbrellas—think structural analysis for naval vessels or software engineering for comms systems—fall under this if CUI is part of the equation.
- R&D and Innovation Labs: Academic spin-offs, private research entities, or tech startups collaborating on DoD-funded projects (e.g., via SBIR grants) need Level 2 if they’re accessing or generating CUI. This is crucial for maintaining eligibility in cutting-edge areas like AI or hypersonics.
- Logistics and Support Operations: Businesses in transportation, warehousing, or supply chain management for defense materials aren’t immune. If your systems process CUI-laden manifests, tracking data, or compliance docs, certification is on the horizon.
- Miscellaneous: Small and mid-sized businesses, which make up most of the DIB supply chain, are particularly vulnerable if they delay action on compliance. Primes are increasingly flowing down requirements to avoid supply-chain risks.
- Exemptions: Exemptions remain limited (e.g., pure COTS with no CUI), but even these are shrinking as flow-downs become standard.
What Does This Mean?
In short, if your work involves DoD contracts and sensitive unclassified information, CMMC likely applies. Exemptions are narrow, primarily for purely commercial off-the-shelf (COTS) items with no CUI involvement. Even these are becoming rarer as primes flow down requirements.
The stakes are clear: Non-compliance can result in loss of eligibility for new awards, delayed contract execution, or exclusion from opportunities altogether. On the positive side, achieving certification strengthens your cybersecurity, builds trust with primes and the DoD, and positions your company as a reliable partner in a competitive market.
The Phased Rollout: Key CMMC Timelines (as of January 2026)
The DoD is implementing CMMC over four phases spanning three years, with increasing rigor. We are currently in Phase 1 (November 10, 2025 – November 9, 2026):
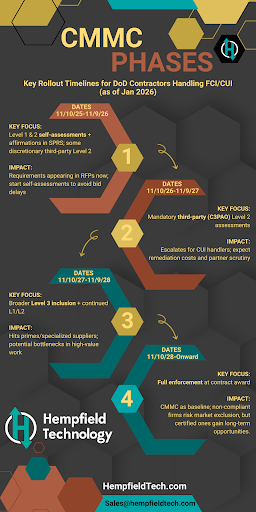
- Phase 1: November 10, 2025 – November 9, 2026 (Ongoing) Focus:
Introduction of CMMC Level 1 (for Federal Contract Information – FCI) and Level 2 (for CUI) requirements in an increasing number of DoD solicitations. Most involve self-assessments with affirmations submitted to SPRS, but the DoD may require third-party assessments for select Level 2 contracts at its discretion. Impact on DIB: Small and mid-sized contractors are seeing CMMC clauses in RFPs now, potentially delaying awards if assessments aren’t complete. Primes may start flowing down requirements to subs, pressuring the entire supply chain to demonstrate basic compliance. This phase affects job sustainment and innovation, as non-compliant firms risk exclusion from bids. For example, if your business handles CUI in manufacturing or IT services, expect to prioritize self-assessments to maintain eligibility. - Phase 2: November 10, 2026 – November 9, 2027 Focus: Shift to mandatory third-party assessments for Level 2 in applicable contracts, while Level 1 remains self-assessed. Level 3 (advanced resilience) may appear in some high-priority solicitations. Impact on DIB: This escalates the stakes for CUI handlers—the bulk of the supply chain. Third-party audits mean external validation, which could reveal gaps and lead to remediation costs. Subcontractors might face tighter scrutiny from primes, potentially reshaping partnerships. Businesses in engineering, R&D, or logistics with CUI exposure will need certified assessors, impacting budgets and timelines for contract pursuits.
- Phase 3: November 10, 2027 – November 9, 2028 Focus: Full integration of Level 3 assessments (conducted by DoD’s Defense Industrial Base Cybersecurity Assessment Center – DIBCAC) into relevant contracts, alongside continued Level 1 and 2 enforcement. Impact on DIB: Aimed at sensitive programs (e.g., weapons systems or classified-adjacent work), this phase hits primes and specialized suppliers hardest. It could bottleneck high-value contracts if assessment capacity is limited, affecting revenue streams and requiring deeper investments in controls like advanced threat hunting.
- Phase 4: Starting November 10, 2028 (Full Implementation) Focus: CMMC certification required at the time of award for all applicable DoD contracts—no exceptions for new awards. Certifications must be maintained, with triennial reassessments. Impact on DIB: This normalizes CMMC as a baseline for DoD business, similar to ISO standards in other sectors. Non-compliant companies could be locked out entirely, leading to market consolidation. On the upside, certified firms gain trust and access to more opportunities, fostering long-term stability. For many contractors, especially those handling CUI, the window to prepare is narrowing. Level 2 readiness often takes 6–18 months, depending on your current cybersecurity posture, so starting now is critical to avoid disruptions.
Looking Ahead
Getting compliant isn’t just about meeting a mandate—it’s an opportunity to fortify your defenses against real-world threats while differentiating your business. In upcoming parts, we’ll dive deeper into the compliance process (including the 14 NIST SP 800-171 control families), practical steps to achieve certification, and proven strategies for smart scoping to reduce your in-scope environment and associated controls.
At Hempfield Technology, we’ve guided defense contractors through these requirements successfully, including helping one client achieve CMMC Level 2 certification. We’ll share more about those experiences as the series progresses—after laying the foundational knowledge first.
If CMMC requirements are appearing in your recent RFPs or contracts, or if you’re unsure about your exposure, reach out or comment below. What’s one specific concern on your radar right now—scope determination, timelines, or something else? We’re here to help navigate this together.
Stay tuned for Part 3: We dive into the actual compliance control Families and overview the implications of each inside of your organization.